Adversarial Machine Learning Course
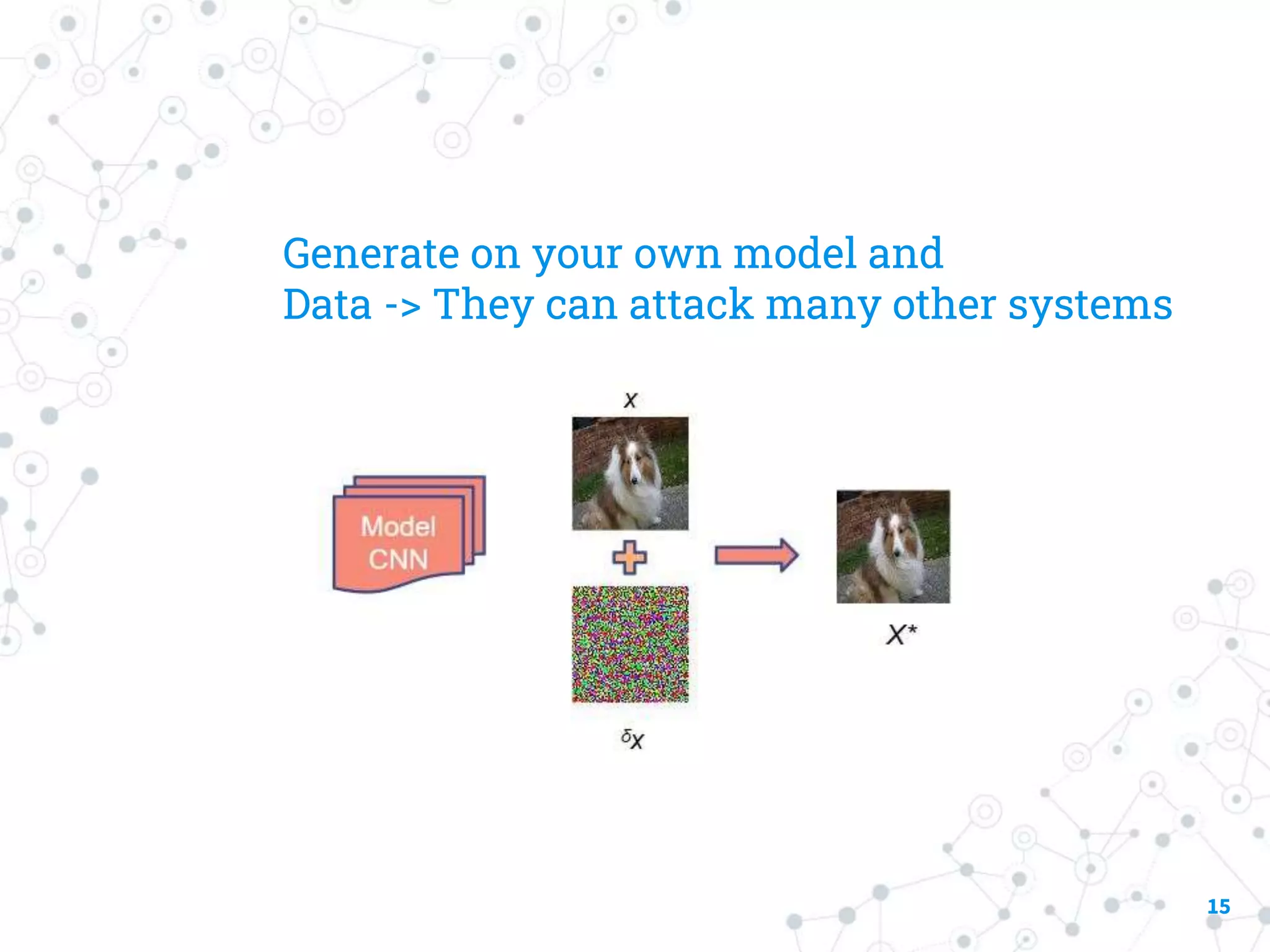
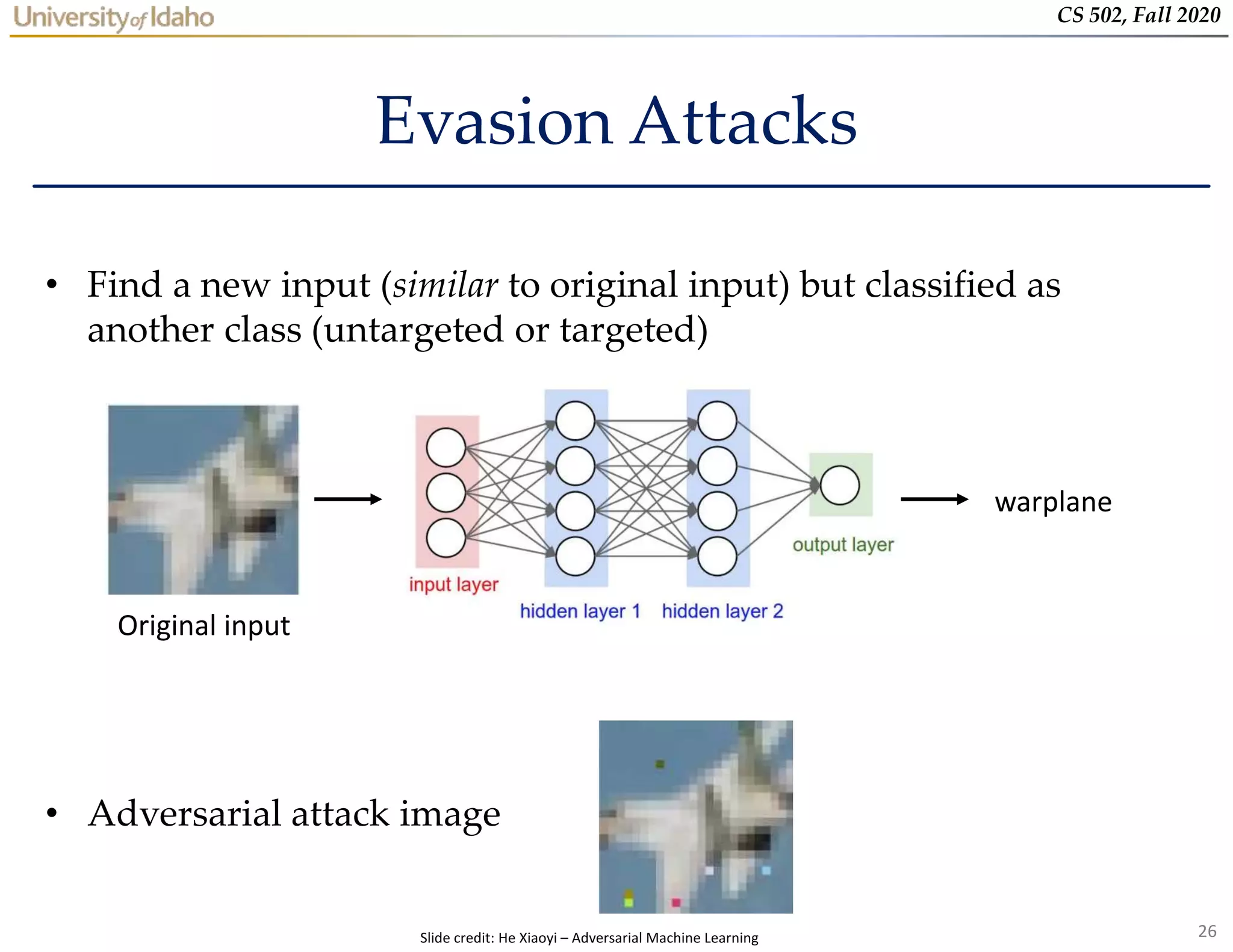
Adversarial Machine Learning Course - Nist’s trustworthy and responsible ai report, adversarial machine learning: Certified adversarial machine learning (aml) specialist (camls) certification course by tonex. Then from the research perspective, we will discuss the. While machine learning models have many potential benefits, they may be vulnerable to manipulation. The particular focus is on adversarial examples in deep. This nist trustworthy and responsible ai report provides a taxonomy of concepts and defines terminology in the field of adversarial machine learning (aml). In this course, which is designed to be accessible to both data scientists and security practitioners, you'll explore the security risks. The particular focus is on adversarial attacks and adversarial examples in. Explore adversarial machine learning attacks, their impact on ai systems, and effective mitigation strategies. Cybersecurity researchers refer to this risk as “adversarial machine learning,” as. Elevate your expertise in ai security by mastering adversarial machine learning. This nist trustworthy and responsible ai report provides a taxonomy of concepts and defines terminology in the field of adversarial machine learning (aml). Explore the various types of ai, examine ethical considerations, and delve into the key machine learning models that power modern ai systems. Certified adversarial machine learning (aml) specialist (camls) certification course by tonex. The course introduces students to adversarial attacks on machine learning models and defenses against the attacks. Thus, the main course goal is to teach students how to adapt these fundamental techniques into different use cases of adversarial ml in computer vision, signal processing, data mining, and. With emerging technologies like generative ai making their way into classrooms and careers at a rapid pace, it’s important to know both how to teach adults to adopt new. This course first provides introduction for topics on machine learning, security, privacy, adversarial machine learning, and game theory. Embark on a transformative learning experience designed to equip you with a robust understanding of ai, machine learning, and python programming. Generative adversarial networks (gans) are powerful machine learning models capable of generating realistic image,. While machine learning models have many potential benefits, they may be vulnerable to manipulation. The particular focus is on adversarial attacks and adversarial examples in. In this course, which is designed to be accessible to both data scientists and security practitioners, you'll explore the security risks. What is an adversarial attack? Adversarial machine learning focuses on the vulnerability of manipulation. What is an adversarial attack? Thus, the main course goal is to teach students how to adapt these fundamental techniques into different use cases of adversarial ml in computer vision, signal processing, data mining, and. The particular focus is on adversarial attacks and adversarial examples in. While machine learning models have many potential benefits, they may be vulnerable to manipulation.. With emerging technologies like generative ai making their way into classrooms and careers at a rapid pace, it’s important to know both how to teach adults to adopt new. This nist trustworthy and responsible ai report provides a taxonomy of concepts and defines terminology in the field of adversarial machine learning (aml). The particular focus is on adversarial examples in. The course introduces students to adversarial attacks on machine learning models and defenses against the attacks. Gain insights into poisoning, inference, extraction, and evasion attacks with real. Cybersecurity researchers refer to this risk as “adversarial machine learning,” as. In this course, which is designed to be accessible to both data scientists and security practitioners, you'll explore the security risks. A. Embark on a transformative learning experience designed to equip you with a robust understanding of ai, machine learning, and python programming. Suitable for engineers and researchers seeking to understand and mitigate. Explore the various types of ai, examine ethical considerations, and delve into the key machine learning models that power modern ai systems. Adversarial machine learning focuses on the vulnerability. Gain insights into poisoning, inference, extraction, and evasion attacks with real. Generative adversarial networks (gans) are powerful machine learning models capable of generating realistic image,. Complete it within six months. The course introduces students to adversarial attacks on machine learning models and defenses against the attacks. Nist’s trustworthy and responsible ai report, adversarial machine learning: The course introduces students to adversarial attacks on machine learning models and defenses against the attacks. Certified adversarial machine learning (aml) specialist (camls) certification course by tonex. Nist’s trustworthy and responsible ai report, adversarial machine learning: What is an adversarial attack? Claim one free dli course. We discuss both the evasion and poisoning attacks, first on classifiers, and then on other learning paradigms, and the associated defensive techniques. Whether your goal is to work directly with ai,. Cybersecurity researchers refer to this risk as “adversarial machine learning,” as. Elevate your expertise in ai security by mastering adversarial machine learning. This seminar class will cover the theory. Apostol vassilev alina oprea alie fordyce hyrum anderson xander davies. Thus, the main course goal is to teach students how to adapt these fundamental techniques into different use cases of adversarial ml in computer vision, signal processing, data mining, and. The course introduces students to adversarial attacks on machine learning models and defenses against the attacks. Nist’s trustworthy and responsible. The particular focus is on adversarial examples in deep. Explore adversarial machine learning attacks, their impact on ai systems, and effective mitigation strategies. In this course, students will explore core principles of adversarial learning and learn how to adapt these techniques to diverse adversarial contexts. Whether your goal is to work directly with ai,. Complete it within six months. Suitable for engineers and researchers seeking to understand and mitigate. It will then guide you through using the fast gradient signed. Thus, the main course goal is to teach students how to adapt these fundamental techniques into different use cases of adversarial ml in computer vision, signal processing, data mining, and. The particular focus is on adversarial attacks and adversarial examples in. Whether your goal is to work directly with ai,. Generative adversarial networks (gans) are powerful machine learning models capable of generating realistic image,. This seminar class will cover the theory and practice of adversarial machine learning tools in the context of applications such as cybersecurity where we need to deal with intelligent. Up to 10% cash back analyze different adversarial attack types and assess their impact on machine learning models. This course first provides introduction for topics on machine learning, security, privacy, adversarial machine learning, and game theory. The course introduces students to adversarial attacks on machine learning models and defenses against the attacks. Cybersecurity researchers refer to this risk as “adversarial machine learning,” as. Nist’s trustworthy and responsible ai report, adversarial machine learning: Adversarial machine learning focuses on the vulnerability of manipulation of a machine learning model by deceiving inputs designed to cause the application to work. In this course, which is designed to be accessible to both data scientists and security practitioners, you'll explore the security risks. This nist trustworthy and responsible ai report provides a taxonomy of concepts and defines terminology in the field of adversarial machine learning (aml). While machine learning models have many potential benefits, they may be vulnerable to manipulation.Adversarial machine learning PPT
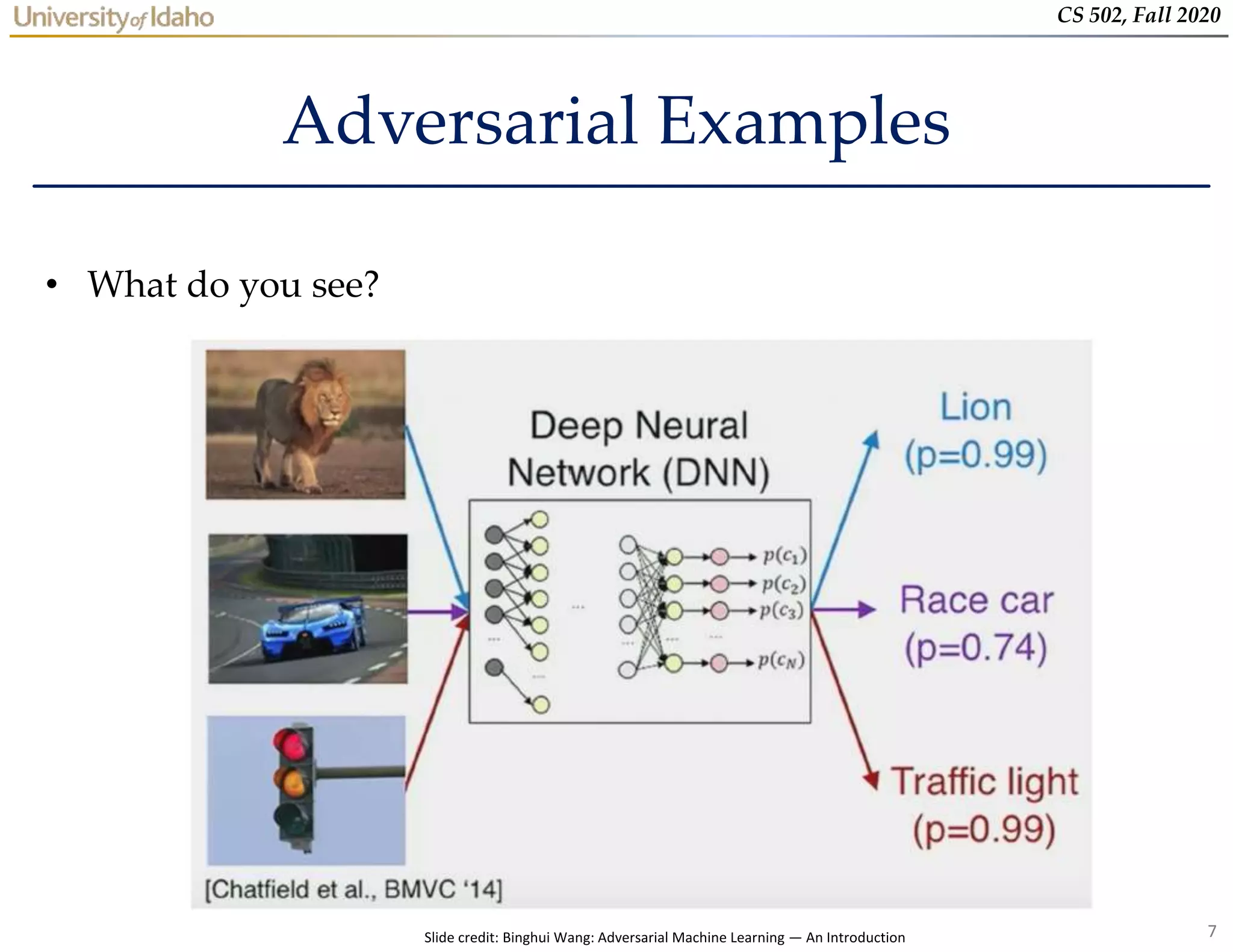
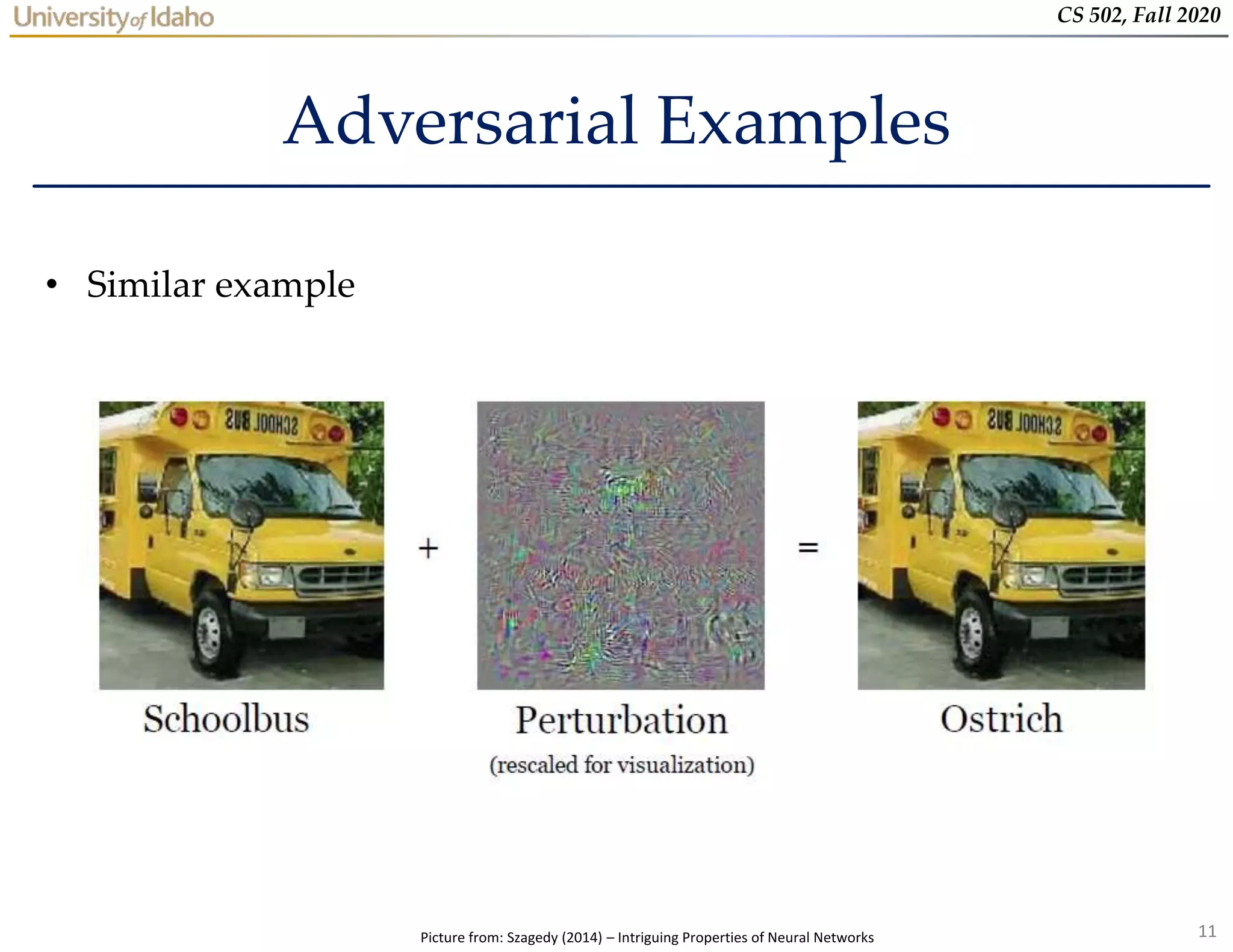
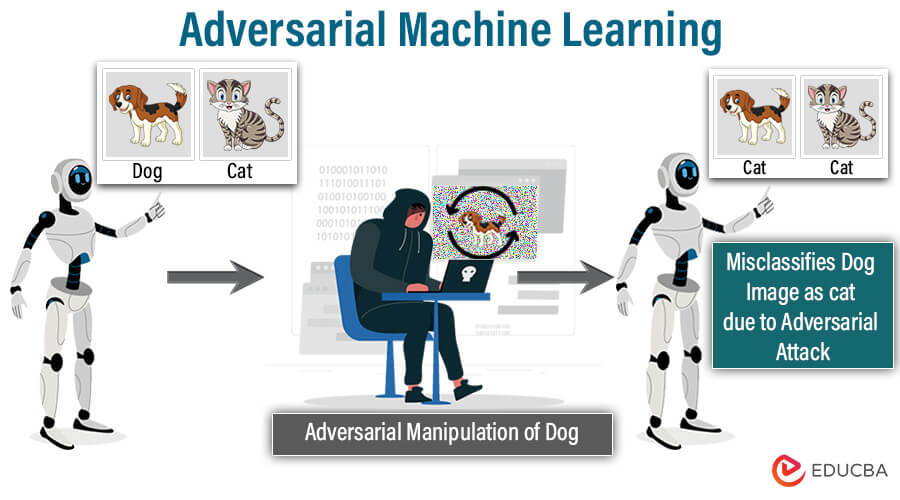
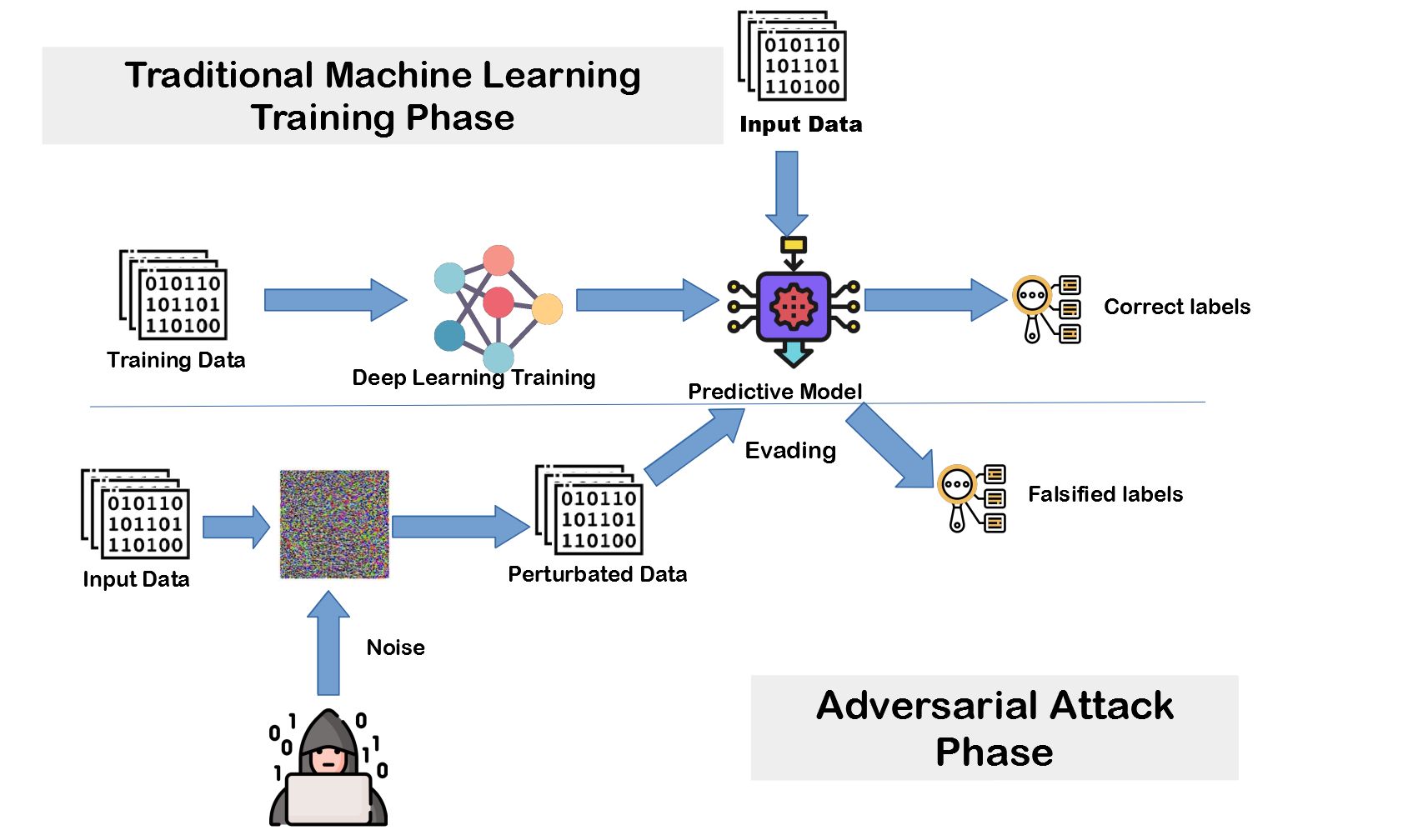
What is Adversarial Machine Learning? Explained with Examples
Adversarial Machine Learning Printige Bookstore
Lecture_1_Introduction_to_Adversarial_Machine_Learning.pptx
Lecture_1_Introduction_to_Adversarial_Machine_Learning.pptx
Adversarial Machine Learning A Beginner’s Guide to Adversarial Attacks
Lecture_1_Introduction_to_Adversarial_Machine_Learning.pptx
Lecture_1_Introduction_to_Adversarial_Machine_Learning.pptx
Exciting Insights Adversarial Machine Learning for Beginners
What Is Adversarial Machine Learning
Gain Insights Into Poisoning, Inference, Extraction, And Evasion Attacks With Real.
Learn About The Adversarial Risks And Security Challenges Associated With Machine Learning Models With A Focus On Defense Applications.
An Adversarial Attack In Machine Learning (Ml) Refers To The Deliberate Creation Of Inputs To Deceive Ml Models, Leading To Incorrect.
Claim One Free Dli Course.
Related Post: